Understanding the Bash Fork Bomb: A Breakdown of :(){ :|:& };:
In the realm of Linux and Unix systems, the concept of a fork bomb is a classic example of a denial-of-service (DoS) attack that exploits the system's process creation capabilities. Among the many ways to implement a fork bomb, the Bash fork bomb :(){ :|:& };: stands out for its brevity and effectiveness. This seemingly cryptic one-liner can bring even a powerful machine to its knees by overwhelming it with an exponentially growing number of processes. In this blog post, we'll delve into the intricacies of this fork bomb, exploring how it works and why it is so potent.
Detailed Explanation
Let's break down the Bash fork bomb :(){ :|:& };: step by step to understand its mechanics:
Function Definition
`:()`
This defines a function named :. In Bash, functions can be named almost anything, including special characters. Here, : is chosen as the function name.
Function Body
`{ :|:& }`
The body of the function is enclosed in curly braces {}. Inside the body, the function calls itself twice and pipes the output to itself:
:: This calls the function:recursively.|: This pipes the output of the first call to the function back into itself.&: This puts each call in the background, allowing the parent process to continue executing and thus not waiting for the child processes to complete.
Function Termination and Execution
`;:`
The semicolon ; marks the end of the function definition. The final : executes the newly defined function.
Putting it all together, the sequence :(){ :|:& };: does the following:
- Defines a function
:that calls itself twice in the background for every invocation. - Immediately invokes the function
:after defining it.
How the Fork Bomb Works
When the function : is executed, it starts two child processes of itself, each of which again starts two more child processes, and so on. This creates an exponential growth in the number of processes. Here's a step-by-step outline of the process creation:
- The initial function call
:is made. - The function
:creates two child processes, each calling:again. - Each of these child processes further creates two more processes, leading to 4 new processes.
- This process continues exponentially, doubling the number of processes at each step.
Since each invocation happens in the background due to the &, the parent processes do not wait for the children to finish, allowing the system to quickly become overwhelmed by the sheer number of processes. This results in resource exhaustion, where the system runs out of available process slots, CPU time, and memory, effectively leading to a denial of service.
Preventing and Mitigating Fork Bombs
To protect a system from fork bombs, administrators can implement several safeguards:
Limit the Number of Processes
Use the ulimit command to restrict the maximum number of processes a user can create:
`ulimit -u 100`
This sets a limit of 100 processes per user, preventing the exponential growth characteristic of a fork bomb.
Monitor System Resources
Regularly monitor system resources and process counts using tools like top, htop, and ps to detect unusual activity early. Automate alerts for unusual spikes in process creation and CPU usage using tools such as Nagios, Zabbix, or Prometheus.
Educate Users
Educate users about the risks of running unknown or untrusted scripts. Promote best practices for writing safe shell scripts. Moreover, implement strict policies regarding script execution and process management to reduce the risk of accidental or intentional misuse.
Use Control Groups (cgroups)
In more advanced setups, Linux control groups (cgroups) can be used to limit and isolate resource usage (CPU, memory, I/O, etc.) for groups of processes. This can prevent a single user or group from consuming all system resources. For systems using systemd, leverage its integration with cgroups to manage resources more effectively by setting limits in unit files.
Implement Security Enhancements
Apply general security hardening techniques to reduce the system's attack surface. This includes keeping the system and software up to date, using firewalls, and employing security modules like SELinux or AppArmor. Restrict the use of privileged accounts and enforce the principle of least privilege.
Summary
The Bash fork bomb :(){ :|:& };: is a powerful example of how a simple script can exploit process creation to cause a denial-of-service attack. By defining a recursive function that calls itself multiple times in the background, it rapidly consumes system resources, leading to system instability or crashes. Understanding how this fork bomb works helps system administrators implement effective measures to mitigate such attacks, ensuring the stability and security of their systems. Always be cautious when running or allowing the execution of scripts, especially those that can manipulate system processes and resources.
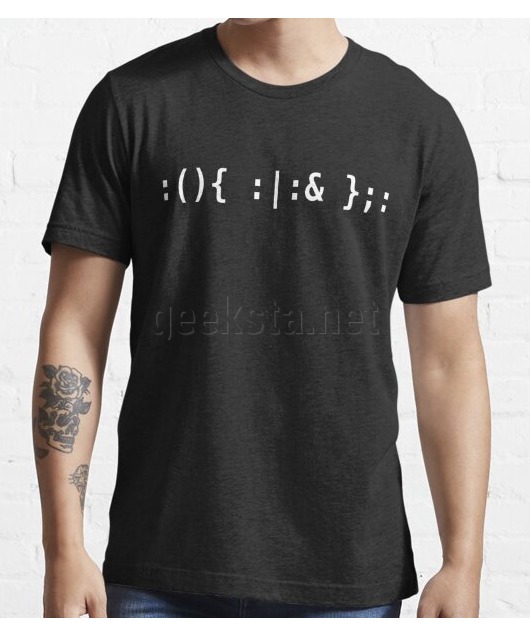
Featured Merch
Latest Posts
- How to Check if an IP Address is Blocked on Linux
- How to Inspect All Cron Jobs on a Linux System: A Sysadmin's Guide
- Building a 3D Elevation Photo Diary with deck.gl
- Thunderbird Keeps Threading Emails? Here's the Fix
- Social Media Dimensions Cheat Sheet 2025
Featured Book
Subscribe to RSS Feed
Published by Ramiro Gómez on . Subscribe to the Geeksta RSS feed to be informed about new posts.
Disclosure: External links on this website may contain affiliate IDs, which means that I earn a commission if you make a purchase using these links. This allows me to offer hopefully valuable content for free while keeping this website sustainable. For more information, please see the disclosure section on the about page.